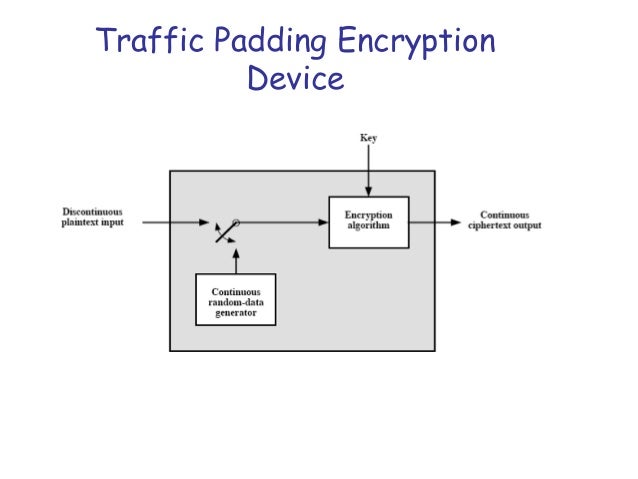
Padding In Network Security. The encrypted message typically reveals the length or approximate length of the message that was encrypted. The value is taken from the list of IP protocol numbers. The message is padded extended so that. Traffic padding may be used to hide the traffic pattern which means to insert dummy traffic into the network and present to the intruder a different traffic pattern.
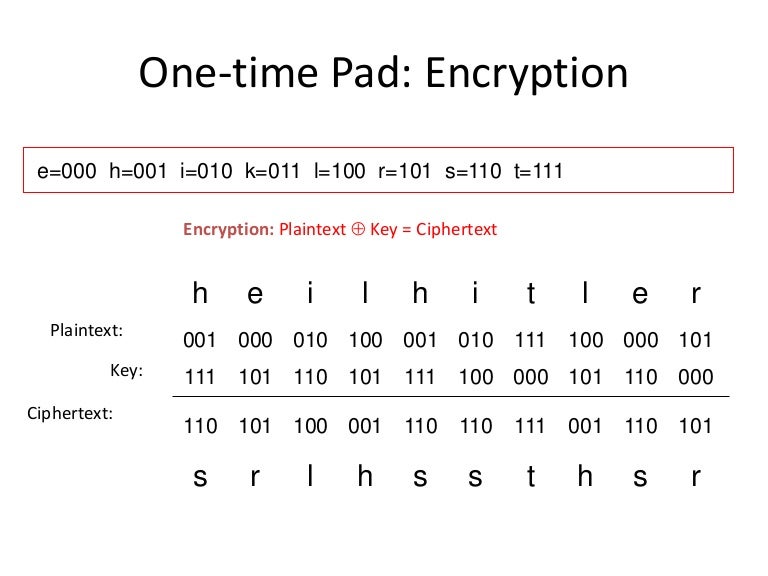
Encryption does not conceal the length of the messages being encrypted. The apparent traffic pattern which is observed by intruder is referred to as a cover mode that hides the real operation mode of the system. Traffic padding mechanisms are used to protect against traffic analysis attacks. For example if the block length is 64 bits and the last block contains only 40 bits 24 bits of padding are added. NETWORK SECURITY - MD5 ALGORITHM - YouTube. Should you believe your personal safety is threatened or that you may be the victim of identity theft or other illegal conduct please contact the local stateprovincial or federal law enforcement agencies directly.
However defenses have been added.
The value is taken from the list of IP protocol numbers. Die padding Eigenschaft ist eine Kurzform für die Innenabstände aller vier Seiten eines Elementes. Consequently traffic padding mechanisms can only be effective if. Should you believe your personal safety is threatened or that you may be the victim of identity theft or other illegal conduct please contact the local stateprovincial or federal law enforcement agencies directly. Network Security IN2101 WS 201516 17 Final Remarks The attack was against CBC mode used in MAC-then-Encode-then-Encrypt mode. We safeguard your personal information from unauthorized access through access control procedures network firewalls and physical security measures.